The Microsoft Authenticator app can be used to sign in to any Azure AD account without using a password. Microsoft Authenticator uses key-based authentication to enable a user credential that is tied to a device, where the device uses a PIN or biometric. Windows Hello for Business uses a similar technology.
- Autofill stores your passwords under your Microsoft account. To get started with autofill on mobile, open the Microsoft Authenticator app, and then sign-in on the Passwords tab with your Microsoft account. If you have passwords saved under your Microsoft account on Microsoft Edge, they will sync to the Authenticator app.
- Use time-based, one-time passcodes The Microsoft Authenticator app also supports the industry standard for time-based, one-time passcodes (also known as TOTP or OTP). Because of that, you can add any online account that also supports this standard to the Microsoft Authenticator app. This will help keep your other online accounts secure.
Microsoft is testing out a new password-management feature in its Authenticator app, which makes the former even more useful as a one-stop shop for all of your account-related information. Microsoft this month announced the 'general availability' commercial release of the 'password management and autofill capability' in the Microsoft Authenticator app for mobile devices.
This authentication technology can be used on any device platform, including mobile. This technology can also be used with any app or website that integrates with Microsoft Authentication Libraries.
People who enabled phone sign-in from the Microsoft Authenticator app see a message that asks them to tap a number in their app. No username or password is asked for. To complete the sign-in process in the app, a user must next take the following actions:
- Match the number.
- Choose Approve.
- Provide their PIN or biometric.
Prerequisites
To use passwordless phone sign-in with the Microsoft Authenticator app, the following prerequisites must be met:
- Azure AD Multi-Factor Authentication, with push notifications allowed as a verification method.
- Latest version of Microsoft Authenticator installed on devices running iOS 8.0 or greater, or Android 6.0 or greater.
- The device on which the Microsoft Authenticator app is installed must be registered within the Azure AD tenant to an individual user.
Note
If you enabled Microsoft Authenticator passwordless sign-in using Azure AD PowerShell, it was enabled for your entire directory. If you enable using this new method, it supercedes the PowerShell policy. We recommend you enable for all users in your tenant via the new Authentication Methods menu, otherwise users not in the new policy are no longer be able to sign in without a password.
Enable passwordless authentication methods
To use passwordless authentication in Azure AD, first enable the combined registration experience, then enable users for the password less method.
Enable the combined registration experience
Registration features for passwordless authentication methods rely on the combined registration feature. To let users complete the combined registration themselves, follow the steps to enable combined security information registration.
Enable passwordless phone sign-in authentication methods
Azure AD lets you choose which authentication methods can be used during the sign-in process. Users then register for the methods they'd like to use.
To enable the authentication method for passwordless phone sign-in, complete the following steps:
- Sign in to the Azure portal with a global administrator account.
- Search for and select Azure Active Directory, then browse to Security > Authentication methods > Policies.
- Under Microsoft Authenticator, choose the following options:
- Enable - Yes or No
- Target - All users or Select users
- Each added group or user is enabled by default to use Microsoft Authenticator in both passwordless and push notification modes ('Any' mode). To change this, for each row:
- Browse to .. > Configure.
- For Authentication mode - Any, Passwordless, or Push
- To apply the new policy, select Save.
User registration and management of Microsoft Authenticator
Users register themselves for the passwordless authentication method of Azure AD by using the following steps:

- Browse to https://aka.ms/mysecurityinfo.
- Sign in, then add the Authenticator app by selecting Add method > Authenticator app, then Add.
- Follow the instructions to install and configure the Microsoft Authenticator app on your device.
- Select Done to complete Authenticator configuration.
- In Microsoft Authenticator, choose Enable phone sign-in from the drop-down menu for the account registered.
- Follow the instructions in the app to finish registering the account for passwordless phone sign-in.
An organization can direct its users to sign in with their phones, without using a password. For further assistance configuring the Microsoft Authenticator app and enabling phone sign-in, see Sign in to your accounts using the Microsoft Authenticator app.
Note
Users who aren't allowed by policy to use phone sign-in are no longer able to enable it within the Microsoft Authenticator app.
Sign in with passwordless credential
A user can start to utilize passwordless sign-in after all the following actions are completed:
- An admin has enabled the user's tenant.
- The user has updated her Microsoft Authenticator app to enable phone sign-in.
The first time a user starts the phone sign-in process, the user performs the following steps:
- Enters her name at the sign-in page.
- Selects Next.
- If necessary, selects Other ways to sign in.
- Selects Approve a request on my Microsoft Authenticator app.
The user is then presented with a number. The app prompts the user to authenticate by selecting the appropriate number, instead of by entering a password.
After the user has utilized passwordless phone sign-in, the app continues to guide the user through this method. Cbse ncert ip book class 12 pdf. However, the user will see the option to choose another method.
Known Issues
The following known issues exist.
Not seeing option for passwordless phone sign-in
In one scenario, a user can have an unanswered passwordless phone sign-in verification that is pending. Clc workbench 12. Yet the user might attempt to sign in again. When this happens, the user might see only the option to enter a password. Download egnyte connect desktop app.
To resolve this scenario, the following steps can be used:
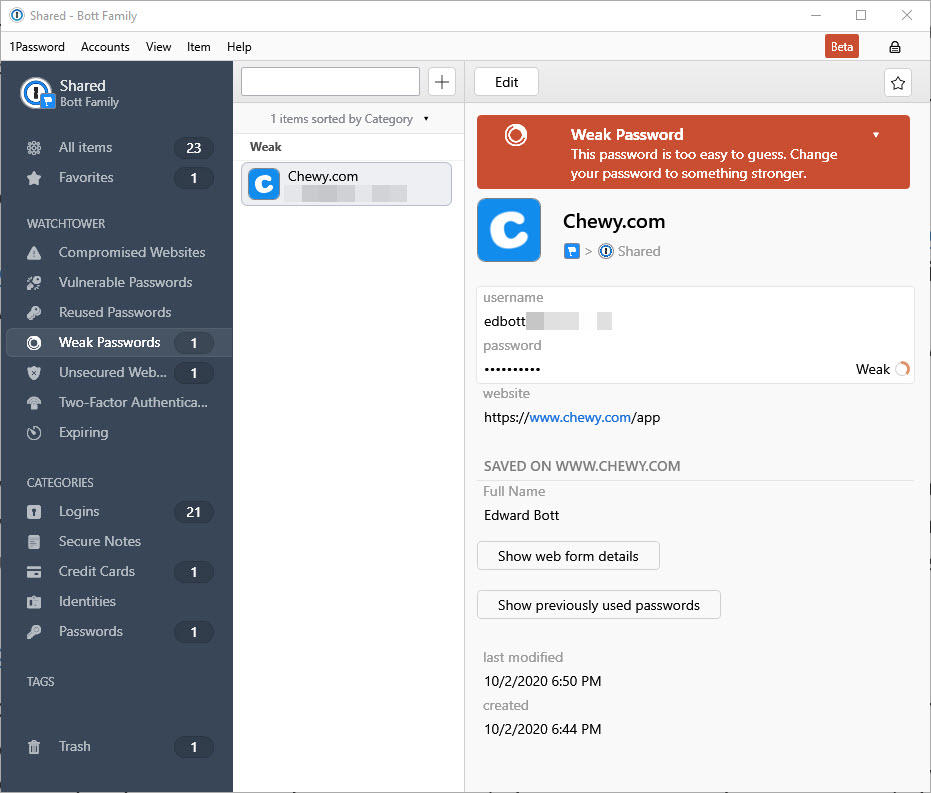
Microsoft Authenticator Password Beta
- Open the Microsoft Authenticator app.
- Respond to any notification prompts.
Then the user can continue to utilize passwordless phone sign-in.
Federated Accounts
When a user has enabled any passwordless credential, the Azure AD login process stops using the login_hint. Therefore the process no longer accelerates the user toward a federated login location.
This logic generally prevents a user in a hybrid tenant from being directed to Active Directory Federated Services (AD FS) for sign-in verification. However, the user retains the option of clicking Use your password instead.
Azure MFA server
An end user can be enabled for multi-factor authentication (MFA), through an on-premises Azure MFA server. The user can still create and utilize a single passwordless phone sign-in credential.
If the user attempts to upgrade multiple installations (5+) of the Microsoft Authenticator app with the passwordless phone sign-in credential, this change might result in an error.
Device registration
Before you can create this new strong credential, there are prerequisites. One prerequisite is that the device on which the Microsoft Authenticator app is installed must be registered within the Azure AD tenant to an individual user.
Currently, a device can only be registered in a single tenant. This limit means that only one work or school account in the Microsoft Authenticator app can be enabled for phone sign-in.
Note
Device registration is not the same as device management or mobile device management (MDM). Device registration only associates a device ID and a user ID together, in the Azure AD directory.
Next steps
1password Sign In Without Authenticator App

To learn about Azure AD authentication and passwordless methods, see the following articles:
With all the hype surrounding Authenticator Apps, I decided to enable the Microsoft Authenticator on my personal Microsoft account. Microsoft describes the Authenticator as “More secure. Passwords can be forgotten, stolen, or compromised. With Authenticator, your phone provides an extra layer of security on top of your PIN or fingerprint.” As a naturally curious security professional, I am constantly trying out new security services and decided to test Microsoft’s claims.
I downloaded the Authenticator app and added my personal Microsoft account to it. The app asked for my Microsoft password and email verification code. Note that both of these are vulnerable to a simple phishing attack. I completed the registration process and logged into my account several times using the Authenticator app to verify that it worked. It did. I could log into my account without a password.
My assumption, after enabling the app, was that no one else could log into my account without me approving it first through the Authenticator app. It goes without saying that no one should be able to register another Authenticator app on my behalf without me approving it first with the Authenticator app that I already have.
So I asked a friend to try to add my personal Microsoft account to his Microsoft Authenticator app. After he entered my email address I got a push notification on my mobile device. I opened the push notification on my device and selected “Deny” to deny him from continuing. But my friend was faster and selected “use password instead” on his phone moments before I selected “Deny”. My friend was then able to enter my password and email verification code and successfully register his Microsoft Authenticator using my account. Microsoft completely ignored me pushing the Deny button and didn’t provide any feedback that a new Authenticator app was registered on my behalf. Microsoft Authenticator would not prevent a criminal from accessing an account once they have obtained a username and password.
After this experiment we were both able to log into my account, each with our own phones. But what happens if one of us chooses Allow and the other chooses Deny? Apparently first to click wins. If the attacker tries to log in and clicks Approve first, the victim can click Deny but it won’t matter – the attacker will get in and once again – no indication is sent to the victim that someone got in.
Where was the extra layer of security that Microsoft Authenticator claimed? While the Microsoft Authenticator app was easy enough to use (as any Authenticator App), is it simply providing a false sense of security?
Using biometrics and push notifications for security purposes should incorporate many additional layers of security resulting in a dynamic, risk-based approach to authentication and authorization. The best systems carefully assess and correlate a host of indicators and variables from the device and the session in real time to validate the user and revalidate if necessary. In the examples above there were plenty of red flags that should have generated alerts and blocked the imposter before access was provided to the device. If you’re serious about device and system security, continuous adaptive risk should be a foundation to your organization’s IT security infrastructure.
Update: I received a few comments on whether 2FA was enabled or not in my tests above. This is not the point I was trying to make here. Even when 2FA is enabled, attackers can still choose to use Email or SMS as a second factor instead of the Microsoft Authentication App. Both Email and SMS are much weaker in terms of security. I’ll follow up next week with a post explaining how SMS and Email 2FA can be bypassed. My expectation is that once I enable an Authenticator App, attackers should not have an easy way of using SMS or Email instead to login or register another Authenticator App.
